Whether you work in banking, education, or run a small business, your network’s security is essential. After all, an insecure network can result in data breaches, theft, unauthorized access, poor network performance, a tarnished reputation, and more. To better understand the state of your network and bolster your network’s defense against current and potential threats, consider using network vulnerability scanners or detection tools to quickly detect existing loopholes.
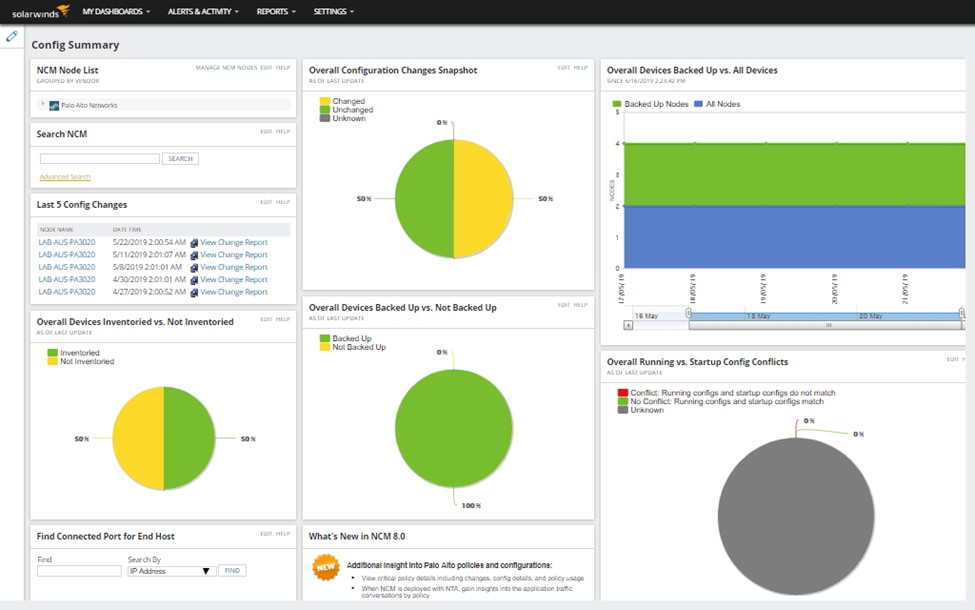
In this article, I’ll go over what network vulnerability scanning is, the key features of network vulnerability scanners, the causes of security vulnerabilities and how to manage them, and the benefits of using a network scanner, as well as five of the best tool options. Though it isn’t a traditional network scanner, SolarWinds® Network Configuration Manager (NCM) can be the right choice for detecting network vulnerabilities. Offering network auditing, network automation, network inventory, vulnerability assessment, and more, NCM is ideal for many organizations. Top 5 Network Vulnerability ScannersWhat Is Network Vulnerability Scanning?
What Are The Key Features Of A Network Vulnerability Scanner?
What Causes Security Vulnerabilities?
What Are Some Top Vulnerability Management Techniques?
What Are The Benefits Of Using A Network Vulnerability Scanner?
Best 5 Network Vulnerability Scanning and Detection Tools
1. SolarWinds® Network Configuration Manager (Free Trial)
3. Intruder Vulnerability Scanner
5. Pentest Tools Network Vulnerability Scanner
Final Thoughts On Network Vulnerability Scanners
What Is Network Vulnerability Scanning?
Network vulnerability scanning can help you identify vulnerabilities in your network, devices, and applications, giving you the information you need to better defend your organization against intruders. Several types of vulnerability scans are at your disposal, including external, internal, comprehensive, and limited scans. Carrying out an external vulnerability scan can help you identify and resolve security vulnerabilities that bad actors can exploit to gain access to your network. In contrast, internal vulnerability scans can help you detect the threats posed by those who have already penetrated your perimeter defenses, as well as malware within your network, any disgruntled employees who happen to be trusted users, and others who have gained access to your network. You can also conduct comprehensive or limited vulnerability scans to gain a more complete understanding of your network. Comprehensive scans will examine printers, switches, firewalls, servers, laptops, phones, software, open ports, and more. However, these scans require bandwidth, so limited scans may be better in certain situations.What Are The Key Features Of A Network Vulnerability Scanner?
The right network vulnerability scanner software can make all the difference. Try to use one that can:Provide accurate information
An inaccurate scanner can send you on wild goose chases after vulnerabilities that don’t exist or cause you to overlook genuine security threats, so it’s crucial to have an accurate, comprehensive scanner.Categorize vulnerabilities
A network vulnerability assessment tool capable of evaluating risks will help you prioritize your network’s security threats and ensure your team is using its time to combat the most critical vulnerabilities.Take action
A scan can unearth an overwhelming number of risks, so addressing network problems can be an intimidating and time-consuming process. However, the help of a scanner equipped with automated responses to specific vulnerabilities can save you time and stress.Provide reports
Scanners capable of creating quality reports about your network’s security status will save you time when it comes to showing compliance with various regulations.Adapt and scale
Your network is unique and will likely change over time, so adaptability and scalability are essential in any tool.What Causes Security Vulnerabilities?
Combatting security vulnerabilities is challenging because there are several ways to compromise networks. However, there are several common causes behind security vulnerabilities and breaches, including:Account abuse
Insiders can abuse their user privileges, resulting in data leaks or misconfigurations, so it’s vital to carefully assign privileges, examine credentials, and remove unused groups and users from your network.Improper network structure
An open network structure can wreak havoc if an authorized user gains access to your network. Once they’re in, they’ll be able to access every part of the network, so segment your network and pay attention to user group privileges.Unknown devices on the network
Unmanaged or unidentified assets on your network could signal that someone has access to your network who shouldn’t, so you should routinely check which devices have access to your ports.Third-party applications
Third-party applications can be useful but are often riddled with holes and introduce new security vulnerabilities to your network once installed.Poorly configured security settings and infrastructure
Your network security settings and infrastructure can also create security vulnerabilities. Improper management can result in serious risks, so keep an eye on your firewall and operating system configurations.Web configuration errors
Similarly, web configuration errors can introduce security vulnerabilities to your network, so you should be wary of HTTP misconfigurations, expired SSL certificates, distributed denial-of-service attacks, and insecure code.Missing updates
Hackers can easily exploit out-of-date programs and devices to access your network.What Are Some Top Vulnerability Management Techniques?
Should a security vulnerability arise, you’ll want to engage in top network vulnerability management techniques to ensure as little damage is done as possible. Penetration testing will show you how an external threat might access your network to steal data. While it’s expensive and time-consuming, it’s a very effective way of identifying your network’s security gaps. For a less time-consuming option, you might use beach and attack simulation software to regularly and automatically test and validate your network and security measures. While antivirus software only focuses on identifying, preventing, and removing malware, it can still help keep your network safe from threats, such as Trojans, spyware, and ransomware. Similarly, web application scanners take a focused approach and will identify vulnerabilities in your web apps, such as SQL injection, cross-site scripting, and misconfigurations. Configuration management is also key to managing vulnerabilities, as hackers often gain access to networks by exploiting misconfigurations and missing patches. Not only are these risks generally relatively easy to fix, but neglecting to address them can result in noncompliance.What Are The Benefits Of Using A Network Vulnerability Scanner?
With countless potential holes in your network, staying on top of vulnerabilities is challenging. Using network vulnerability scanner software will give you increased visibility over your entire network, helping you quickly pinpoint weaknesses and take action to prevent costly data breaches, even as your network and devices evolve. Beyond simply identifying and providing information about weaknesses in your network, some network vulnerability scanner tools can provide recommendations to mitigate risks or even take action automatically to resolve the issue. A scanner tool can also help you identify applications and systems that fall through the cracks and discover unauthorized devices, systems, and remote access servers on your network. Using network vulnerability assessment tools will enable you to take preventative security measures and actions against current vulnerabilities before it’s too late.Best 5 Network Vulnerability Scanning and Detection Tools
There are countless network vulnerability scanning tools available, but some are better than others. Here are our five picks for the best network vulnerability scanners or configuration management tools with vulnerability detection features on the market today.1. SolarWinds® Network Configuration Manager (Free Trial)
Download Free Trial Learn More
Leave a Reply