Active Directory (AD) is a foundational element of any Microsoft Windows environment because of the part it plays in authentication, access management, account management, and authorization. To ensure the health and efficiency of your Active Directory, it’s crucial for you to engage in proper Active Directory auditing and reporting best practices.
This article will detail essential Active Directory auditing best practices and provide recommendations for the best Active Directory auditing tools.
This article will be useful if you need to know if the computer environment you manage needs an Active Directory security audit. You’ll also learn what elements should be included in an Active Directory audit and what tools you can use for reporting the status of Active Directory services.
For its user-friendliness and comprehensive range of features, SolarWinds® Security Event Manager (SEM) tops our list of the best Active Directory auditing tools. A free trial can be downloaded here.
What Is an Active Directory Security Audit?
Active Directory auditing refers to the practice of collecting information on your Active Directory attributes and objects. You can then analyze this information to determine and report on your AD’s overall health.
An Active Directory security audit is essential to achieving regulatory compliance and robust cybersecurity because it allows you to review access rights to important resources and monitor who is creating new accounts.
However, by default, Active Directory doesn’t audit all your security events. To achieve comprehensive coverage, you must enable the auditing of any notable events to ensure your security event log has accounted for them.
Although Active Directory’s purpose is to simplify an organization’s identity management operations, the visibility limitations of Active Directory’s default settings can cause problems for sysadmins. Fortunately, Active Directory auditing best practices and Active Directory groups best practices can help SysAdmins overcome these problems, which brings us to why you need an Active Directory security audit.
Why Do You Need an Active Directory Security Audit?
Active Directory auditing enables you to significantly reduce security risks by assisting in flagging and remediating any toxic conditions associated with your directory.
Companies perform Active Directory security audits for many reasons, including:
- To protect Active Directory from cybercriminals
- To preserve, protect, and improve IT operations
- To certify compliance
As an example of how an audit might protect a company from cybercrime, an Active Directory security audit might reveal one or more deeply nested groups, which represents a vulnerability an attacker could exploit to access network resources.
In the case of audits helping companies improve IT operations, an audit might expose circular nesting or token bloat, which can hang or slow down applications.
For many institutions, Active Directory auditing is not simply encouraged but required. Regulations like SOX 404 mandate that certain companies implement policies and controls to facilitate the quick identification and rectification of application faults.
Organizations serious about cybersecurity, operational efficiency, and compliance often use a strict Active Directory audit policy and adhere to Active Directory best practices.
What Should Active Directory Audits Report On?
There are many Active Directory best practices to consider, which leaves people wondering what their Active Directory security audits should be reporting on. To help you separate the inconsequential from the critical, here’s a list of the top 10 Active Directory elements you should be auditing.
Access rights and security permissions
Object modifications
Object deletions
Object audit and ownership settings
Inactive accounts
Logoff and login events
Account lockouts
Schema configuration security
Password modifications
Activities performed by privileged users
1. Access Rights and Security Permissions
If privileged users are exploiting their permissions, they may leak confidential data, either maliciously or unknowingly. Maintaining a policy of minimum privilege, which involves only equipping users with necessary access rights, is an important best practice for Active Directory sites and services.
2. Object Modifications
Unauthorized, undetected, and ongoing object attribute modifications increase the likelihood of someone or something compromising your directory. The native Event Viewer functionality can make auditing object modifications challenging, but fortunately, plenty of Active Directory auditing tools can help you audit object modifications.
3. Object Deletions
Restoring accidentally or purposefully deleted objects in your Active Directory is a frustrating task for IT admins. Reporting on object deletions in your Active Directory security audit keeps you informed of deletions, so you can restore them as quickly as possible.
4. Object Audit and Ownership Settings
Ownership monitoring, though often overlooked, is one of the most important Active Directory auditing best practices. Proactively managing and regularly reviewing access controls and security restrictions plays a crucial role in broader network control and should factor into your Active Directory auditing and reporting processes.
5. Inactive Accounts
When accounts fall dormant or become obsolete, your AD becomes vulnerable to hackers hoping to infiltrate your systems. Despite this, inactive accounts often accumulate unnoticed. To ensure your directory remains secure, you should include inactive accounts in your Active Directory security audits and reporting activities.
6. Logoff and Login Events
Another valuable Active Directory auditing best practice involves monitoring logoff and login events, such as failed login attempts and concurrent logins. When these events stray from the norm, they should be considered suspicious activity and investigated.
7. Account Lockouts
Although account lockouts can be reasonably common, caused by multiple failed attempts to log in or stale credentials, numerous failed login attempts could indicate a cyberattack. Because of this, account lockouts must be investigated and verified as legitimate before you re-enable accounts. It’s also best practice to examine whether the account lockout will impact any other activities or objects during your audit.
8. Schema Configuration Security
Ensuring schema configuration security is another critical Active Directory best practice. Securing your network data and assets will help you prevent insider abuse and data leakages.
9. Password Modifications
Cybercriminals may be able to steal data if they manage to infiltrate an account in your Active Directory. In many cases, you can prevent intrusions of this nature by implementing password policies and auditing password modification attempts.
10. Activities Performed by Privileged Users
Privileged users are often responsible for vulnerabilities in your Active Directory, intentionally or otherwise, which is why it’s essential for the activities of privileged users to be traceable and carefully monitored.
Why Use Active Directory Reports Software for Your Auditing Needs?
The features provided by Active Directory reports software can help organizations streamline and simplify their monitoring and reporting processes.
Although different reports software will offer differing functionality, here are some notable features to look out for when considering implementing Active Directory auditing tools.
Access Comprehensive Insight into Security Gaps
An effective Active Directory auditing tool will provide you with deep insight into where security gaps might lie in your directory. With the right tool, you will gain visibility into user access levels, user activities, and user accounts, allowing you to identify and rectify security gaps in your AD environment. Comprehensive insight of this nature allows you to resolve vulnerabilities before they can be exploited by hackers.
Monitor Active Directory Modifications in Real Time
Active Directory doesn’t include native alerting functions to update your team on system health—which means if one of your replication functions has degraded, you may not discover this issue until it has impacted users. Active Directory monitoring software allows you to monitor your system’s health in real time and alert you to problems, so you can resolve them before users are affected. Real-time insights maximize visibility, improve security posture, and play an essential role in mitigating insider threats.
Monitor Access Rights and Group Memberships
The ability to monitor group memberships and access rights to your AD file servers is critical to effective risk assessment and management. Some Active Directory auditing tools provide insight into the level of security risk posed by users, empowering you to halt insider threats before they have a broader impact on your organization.
Track Deactivated and Inactive Users
Provisioning and de-provisioning accounts significantly contributes to administrator workload. The right Active Directory security audit tool can automate this process for you, mitigating the need to log in to the Active Directory server and rely on native functionality to create users manually.
When selecting an Active Directory auditing tool for your organization, keep an eye out for role-specific templates that allow you to automate permissions; this functionality can massively expedite your account provisioning processes, saving you time and resources in the long term.
Certify Compliance
If your organization is ever subject to an investigation, an auditor may require comprehensive reports to validate your compliance with relevant regulatory requirements. Active Directory reporting to satisfy an auditor can be time-consuming and complex without the right tools. Fortunately, many Active Directory auditing tools feature integrated compliance reporting functionalities. Some include audit-ready reports designed to support a range of industry-specific standards, such as GDPR and HIPAA.
Best Practices for Active Directory Auditing
An effective Active Directory audit can be broken down into five steps.
Step One: Review and Analyze
Thoroughly survey your Active Directory and report on anything that might be considered suspicious, an area of vulnerability, or an outright threat to the environment. Here are some examples of what you might review and take note of during your analysis:
- Who has access rights to organizational units and domain controllers
- The number of groups and accounts in the directory
- If any inactive or deactivated accounts have yet to be de-provisioned
- Whether a policy of least privilege is being adhered to
- The nature of any toxic conditions in the environment
Step Two: Prioritize
Having compiled your findings, the next step is to prioritize remediation tasks based on which conditions pose the greatest threat to the environment and your organization. It’s best practice to conduct a risk assessment at this stage to inform your decision.
Many organizations begin by addressing privileged access issues, which involves reviewing critical objects for any vulnerabilities. Others may start with large group remediation or privileged user access—areas that could harbor direct threats to directory security.
Step Three: Involve Key Stakeholders
To address the priority issues identified in step two, you’ll need to secure the involvement of the appropriate stakeholders. For example, in the case of user access and permissions, you may want to identify and contact whoever manages the relevant groups or users to confirm why they granted specific permissions. This will allow you to determine whether the permissions are justified or represent a threat.
Step Four: Remediate
The order in which you remediate these conditions should align with the order of priorities you established in step two. Although many organizations begin by ensuring adherence to the least privilege policy, you may decide first to prioritize another more urgent course of action.
Step Five: Preserve the Process
Ensure your Active Directory auditing process is repeatable and becomes part of a continuous cycle. To keep your Active Directory healthy, compliant, and secure, you must conduct regular audits. By making the auditing process a part of your wider operations, you can help keep your Active Directory free of vulnerabilities in the long term.
Best Tools for Active Directory Auditing
There are many Active Directory auditing tools available on the market today, but two stand above the rest—SolarWinds Security Event Manager and ManageEngine ADAudit Plus.
1. SolarWinds Security Event Manager
SolarWinds Security Event Manager (SEM) is a security information and event management solution designed to help you quickly demonstrate compliance and improve your overall security posture. This lightweight, affordable tool is user-friendly and includes a great array of features.
As an Active Directory auditing tool, SolarWinds SEM has a lot to offer, including:
- Active Directory events monitoring covering security group creation and deletion, user account creation and deletion, concurrent user logins, failed login attempts, and more
- Azure Active Directory activity log processing, including sign-in logs, provisioning logs, and audit logs
- Integrated compliance reporting, with support for industry-specific regulations such as HIPAA, SOX, and more
- Ability to automate and schedule reports
- Centralized log repository to make validating regulations, controls, and internal policy implementation easier
- Continuous, real-time monitoring of log analytics
- Integrated notifications and alerts to keep you informed of any threats
- User-friendly dashboard for simplified analysis
- Event and log correlation, enabling you to investigate suspicious activity quickly
- Ability to set up event-time correlation rules for initiating active responses when thresholds are triggered
SolarWinds SEM includes all the functionality required to perform regular, comprehensive, and streamlined Active Directory audits, and much more. A fully functional 30-day free trial is available.
2. ManageEngine ADAudit Plus
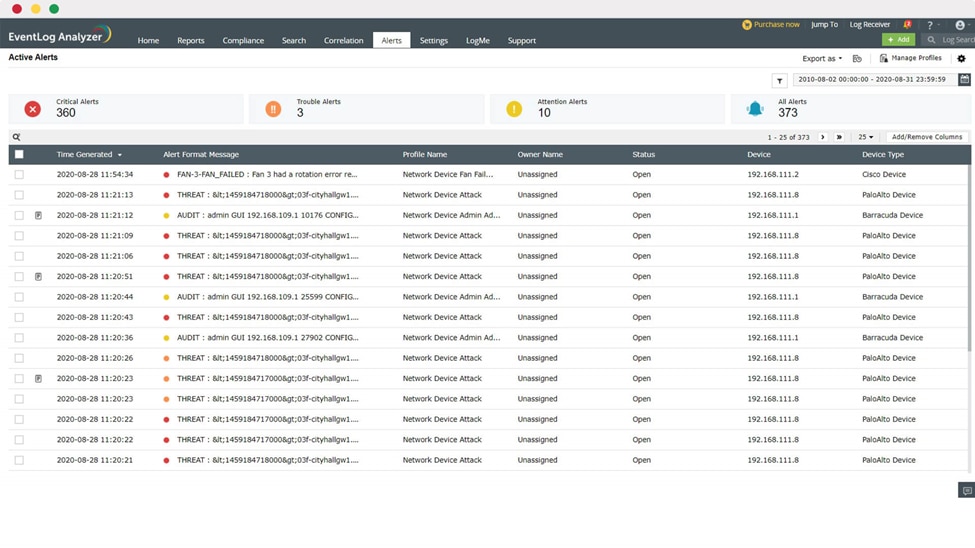
ManageEngine ADAudit Plus is a powerful Active Directory auditing tool that offers real-time insight into user activity and automated insider threats detection.
ADAudit Plus is an especially powerful compliance tool because it includes pre-formatted reports for various standards, such as SOX, GLBA, HIPAA, PCI-DSS, and FISMA. This eliminates the need to create your own reports for demonstrating compliance.
ADAudit Plus has plenty of other impressive features, including:
- Directory modification monitoring, flagging recently created, modified, or deleted GPOs, with a log of all historical changes
- End-user experience regulation with real-time tracking of alterations made to Windows settings
- Instant notifications of unwarranted or suspicious alterations made to your Group Policy settings
- Ability to schedule regular reports on GPO links and who was responsible for them
- Ability to conduct forensic investigations with a complete audit trail
- Account lockout and troubleshooting analysis features
- User login behavior monitoring
The ADAudit Plus custom reporting functionality comes with a steep learning curve. However, with its user-friendly interface and support for automation and scripting, ADAudit Plus should still rank highly on any list of the best Active Directory auditing tools.
If you’d like to give ADAudit Plus a try, you can access a fully functional 30-day free trial here.
Choosing the Best Active Directory Auditing Tool
Although SolarWinds SEM and ManageEngine ADAudit Plus are both powerful tools, SEM has the advantage of user-friendliness. For a comprehensive Active Directory auditing tool with a minimal learning curve, I think SolarWinds SEM is a clear choice. Sign up for a 30-day free trial here.