In IT environments, all software applications and systems produce logs with varying levels of details or context about different events. These log files are automatically generated, and you can see them as a time-stamped record of events. Traditionally, organizations maintained logs locally or in a self-hosted setup. This was done primarily to meet various compliance mandates. If there was a data breach or cyber exploit, logs were considered the first source of information for finding the security lapse or determining who was responsible. This led to the evolution of various advanced tools and practices in security information and event management (SIEM). Though most of this is still true, log analysis is now seen as a crucial exercise in a wide range of IT operations beyond SIEM. We’ll discuss these use cases and list the reasons you should start analyzing your logs.
What Is Log Analysis?
Log files contain event data in a time sequence, giving crucial insights about a system or application’s health and performance. The process of extracting these insights with various analytical and statistical methods is known as log analysis. Though the term is self-explanatory, the methods and tools used to analyze logs have evolved significantly over the years. Unlike the past, when administrators accessed system or server logs with SSH, log analysis is no longer restricted to a few log files. Most organizations have refactored their monolithic applications for microservices architectures. These applications are often deployed in a hybrid, container-based environment, so administrators must monitor log files from a wide range of cloud-based and on-premises resources, including stateless containers and more.
With so many moving components, there’s always a chance of logs getting lost. Managing a large volume of logs for real-time analysis can be a significant challenge and requires dedicated tools. Organizations have to stream logs to a centralized location and store them in a scalable database capable of meeting surges in log volumes. This is where cloud-based log management tools like SolarWinds® Papertrail™ come to the rescue.
Top 5 Benefits of Log Analysis
Reliable IT Operations
Log analyzers can help you troubleshoot software and hardware problems. With constant monitoring, teams can detect and quickly resolve configuration issues, hardware errors, and application bottlenecks. Through log analysis, network administrators can also understand the usual traffic patterns, block malicious traffic, and resolve any network-related issues. Additionally, teams can set up threshold-based alerts to stay on top of their IT environments and ensure oversights aren’t leading to repeated outages or impaired performance.
Performance Improvements
Beyond the troubleshooting stage, organizations can also analyze their logs to optimize their systems and make performance improvements. One of the easiest ways to track performance is to monitor error rates, memory consumption, transaction durations, and similar indicators. By monitoring these indicators, teams can detect issues such as network overload, latency, and more and optimally allocate resources to improve performance. Log analysis often helps reveal bugs in application code capable of impacting system performance without triggering threshold-based alerts.
Optimum Resource Allocation
Logs can also contain crucial data about server performance and utilization. Though there are dedicated server performance monitoring tools available, using logs alongside server metrics gives a more in-depth view of server usage patterns. By looking at historical logs and correlating the data with application exceptions and system errors, teams can identify lingering issues and even predict future trends. These insights can help in capacity planning for optimum server utilization.
Enhanced Security
Log analysis also plays a crucial role in cybersecurity. With logs, security teams can monitor various system activities, endpoints, authentication events, virtual private network (VPN) connections, firewalls, intrusion detection systems, routers, and much more. Organizations can analyze and correlate multiple logs to detect malicious traffic, suspicious user activities, misconfiguration, and policy violations and take remedial actions to counter security threats.
Compliance
Finally, log management and analysis are crucial for meeting HIPAA, PCI DSS, ISO/IEC 27002:2013, NIST 800-137, and several other industry-specific compliance mandates. Organizations can also maintain logs for their internal audits.
How to Analyze Logs Efficiently
No matter which log management tool you’re using, log analysis involves some common steps. The first step is normalizing the log data. Because event logs from different devices and applications vary in format, it’s not easy to query and correlate them. With normalization, all log entries are transformed into a standard format. This is followed by grouping log messages under different fields and tags, which helps organize the data for quick analysis. Visualizing and identifying patterns by analyzing historical data and correlating logs from different sources are the next steps in log analysis.
Log analysis can get more challenging as log volumes grow. Most traditional log viewers and analyzers get sluggish as the workload increases. You’ll need advanced solutions for log analysis capable of performing reliably under varying workloads. Though it’s possible to create a self-hosted setup using open-source tools such as Elasticsearch, Logstash, Fluentd, Kibana, and Grafana, configuring and maintaining these tools can take significant time and effort. To avoid these challenges, organizations often rely on commercial solutions like Papertrail for log management and analytics.
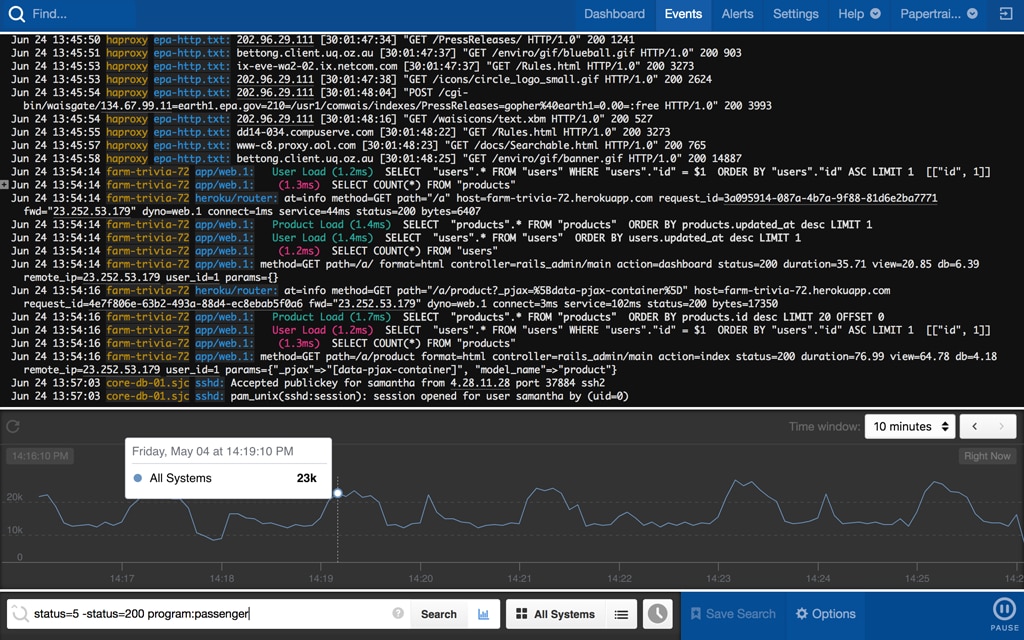
Explore Papertrail for Log Analysis
Papertrail is a cloud-based solution, so you don’t have to invest in hardware and can upgrade to a higher plan at any moment without provisioning worries. The tool can help you search through a large volume of logs and provides results within seconds. You can use simple search operators to explore events of interest, and its real-time event viewer with a live tail feature provides visibility into production environments. You can easily scroll in this viewer, highlight events with different colors, pause the live feed to focus on a message, and skip to a specific time to inspect logs. Moreover, Papertrail helps you detect spikes in log volumes with its log velocity analytics. These spikes are often a sign of critical issues within the IT environment. The tool also integrates easily with popular notification services like Slack, HipChat, and PagerDuty. You can explore the features and advantages of Papertrail with a free trial here.